Using Netstat to Find Active and Listening Ports
Netstat is one of those command-line utilities that seems like it’s been around forever. It’s been a reliable command-line utility to inspect local network connections for a long time. Let’s check out how to use it to find listening and established network connections.
Netstat has many different parameters. This tutorial will only use three of them. To learn more about what netstat can do, run
netstat /?.
Assuming you’re on a Windows PC:
1. Open up an elevated command prompt (cmd.exe).
2. Run netstat -a to find all of the listening and established connections on the PC. By default, netstat only returns listening ports. Using the -a parameter tells netstat to return listening and established connections.
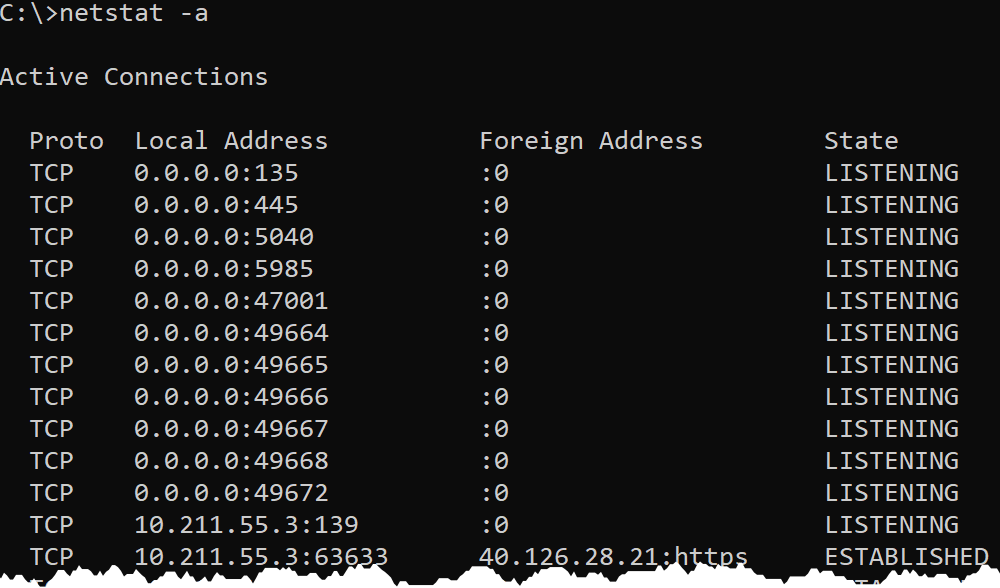
The output above is broken out into four columns:
Proto– shows either UDP or TCP to indicate the type of protocol used.Local Address– shows the local IP address and port that is listening. For many services, this will be 0.0.0.0 for the IP part, meaning it is listening on all network interfaces. In some cases, a service will only listen on a single Network Interface (NIC). In that case, netstat will show the IP address of the NIC. A colon separates the IP address from the port that it is listening on.Foreign Address– shows the remote IP address the local connection is communicating with. If theForeign Addressis0.0.0.0:0, the connection is listening for all IPs and all ports. For established connections, the IP of the client machine will be shown.State– shows the state the port is in, usually this will beLISTENINGorESTABLISHED.
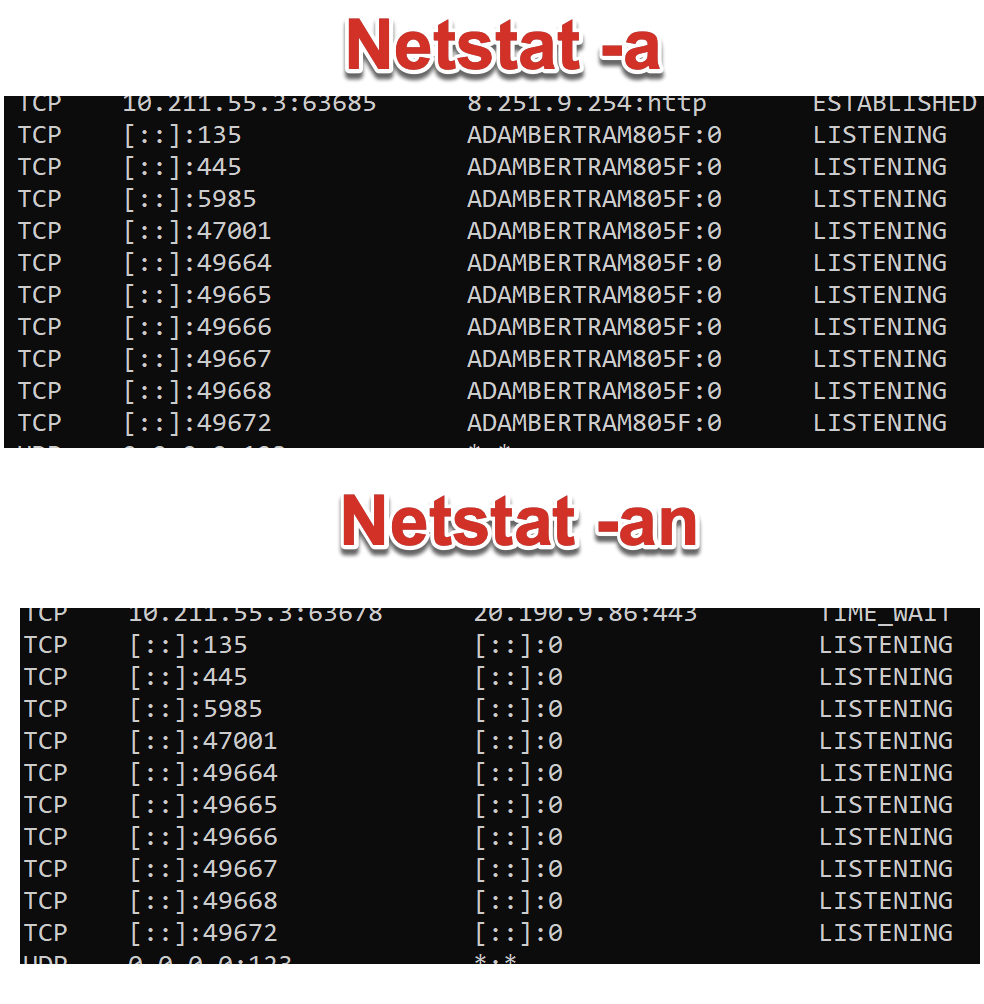
3. Now run netstat -an. You should now see that any
names in the output have been turned into IP addresses. By default,
netstat attempts to resolve many IP addresses to names.
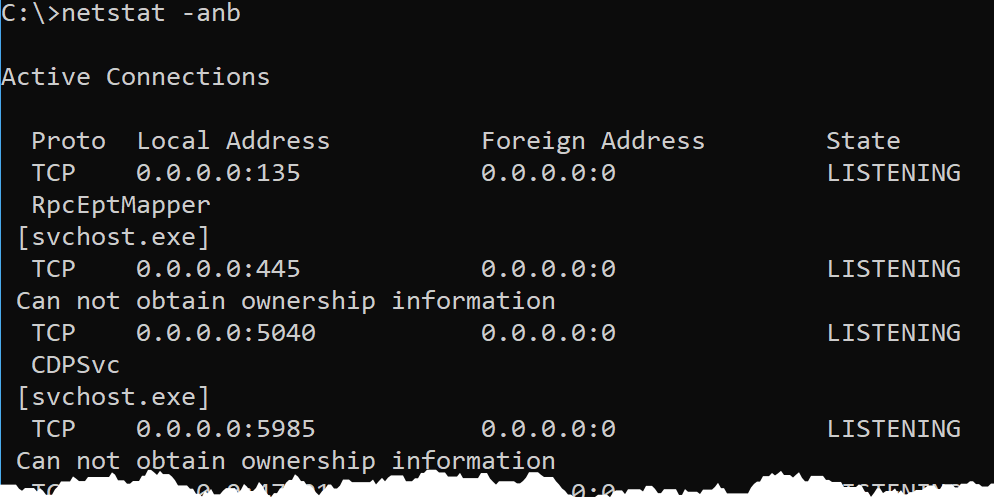
4. Finally, perhaps you’d like to know the Windows processes that are
listening or have these connections open. To find that, use the -b switch.
Using the
-bswitch requires an elevated command prompt or PowerShell prompt. You will get the errorThe requested operation requires elevationif you use the-bswitch in a non-elevated prompt.
How to kill port 443 in windows
taskkill /PID <yourid> /F